Deep Threat Analysis
Enable Visibility Across Cyber Vulnerabilities
Readiness Challenge:
Deep Threat Analysis
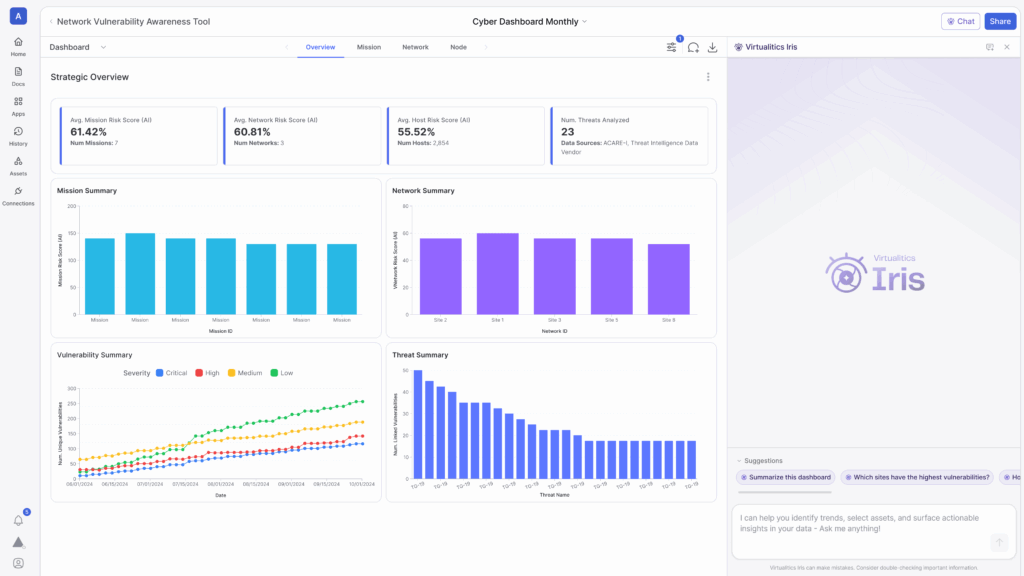
Cyber security analysts are often overloaded with managing massive data streams across disparate systems while reacting to ever-evolving threats. Limited visibility into network vulnerability assessments, threat actor analysis, and critical infrastructure protection can lead to undetected risks and delayed responses.
Fusing these data sources and applying machine learning models allows organizations to predict emerging threats, flag anomalies, and proactively strengthen cyber defenses.

Powered by Virtualitics Integrated Readiness Optimization
AI Insights in IRO Reveal:
What are our vulnerabilities?
Secure your domain. View the overall risk to your networks.
How should we respond?
Focus on what matters. Strategically prioritize hosts and vulnerabilities for effective risk management.
What if?
Stay alert and online. Plan immediate reactions to high-risk events.
What customers are saying about IRO:
Stay Online and Secure with AI-Powered Deep Threat Analysis
Key features addressing areas of critical security and availability impacts:
Multi-Domain Unification
Combine vulnerability scans, threat intelligence feeds, and AI-powered assessments.
Asset Criticality Assessment
Quickly generate reports for every asset ranked by identified critical vulnerabilities and true risk factors.
Threat Group Identification
Protect against potential attacks by matching known threat groups and linked vulnerabilities to those present on your networks.
Rapid Research
Identify hosts that are likely targets through Host Fingerprinting, Host Type Labeling, and Automated Asset Criticality identification.
Deployed at Scale in the Mission Today
Time to Value
From data access to full-scale deployment
Awarded to Virtualitics
Our growing patent portfolio demonstrates our level of investment in AI innovation
IRO Deployments
Across all major military branches
Want to learn more?
Meet With Us